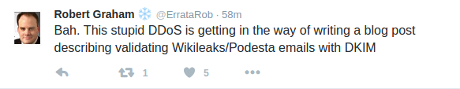
A quick heads up that Robert Graham is working on:
While we wait for that post to appear at Errata Security, you should also take a look at DomainKeys Identified Mail (DKIM).
From the homepage:
DomainKeys Identified Mail (DKIM) lets an organization take responsibility for a message that is in transit. The organization is a handler of the message, either as its originator or as an intermediary. Their reputation is the basis for evaluating whether to trust the message for further handling, such as delivery. Technically DKIM provides a method for validating a domain name identity that is associated with a message through cryptographic authentication.
In particular, review RFC 5585 DomainKeys Identified Mail (DKIM) Service Overview. T. Hansen, D. Crocker, P. Hallam-Baker. July 2009. (Format: TXT=54110 bytes) (Status: INFORMATIONAL) (DOI: 10.17487/RFC5585), which notes:
…
2.3. Establishing Message ValidityThough man-in-the-middle attacks are historically rare in email, it is nevertheless theoretically possible for a message to be modified during transit. An interesting side effect of the cryptographic method used by DKIM is that it is possible to be certain that a signed message (or, if l= is used, the signed portion of a message) has not been modified between the time of signing and the time of verifying. If it has been changed in any way, then the message will not be verified successfully with DKIM.
…
In a later tweet, Bob notes the “DKIM verifier” add-on for Thunderbird.
Any suggestions on scripting DKIM verification for the Podesta emails?
That level of validation may be unnecessary since after more than a week of “…may be altered…,” not one example of a modified email has surfaced.
Some media outlets will keep repeating the “…may be altered…” chant, along with attribution of the DNC hack to Russia.
Noise but it is a way to select candidates for elimination from your news feeds.