The Missouri Attorney General’s office needs to remove St. Louis Prosecuting Attorney Robert P. McCulloch from the Michael Brown case. Then convene a grand jury led to represent the public’s interest and not that of Darren Wilson.
As we saw in Michael Brown Grand Jury – Presenting Evidence Before Knowing the Law, an indictment of Darren Wilson for second degree murder in the death of Michael Brown only requires probable cause (“a reasonable belief that a person has committed a crime”) to find that:
- Darren Wilson (a person)
- intentionally shot (knowingly causes)
- to kill Michael Brown (another person) or
- to inflict serious injury on Michael Brown (another person)
- and Michael Brown dies (death)
It need not be a long and drawn out grand jury like the first one.
Just in case the Missouri Attorney General takes my advice (yeah, right), here is a thumbnail sketch to avoid a repetition of the prior defective grand jury process.
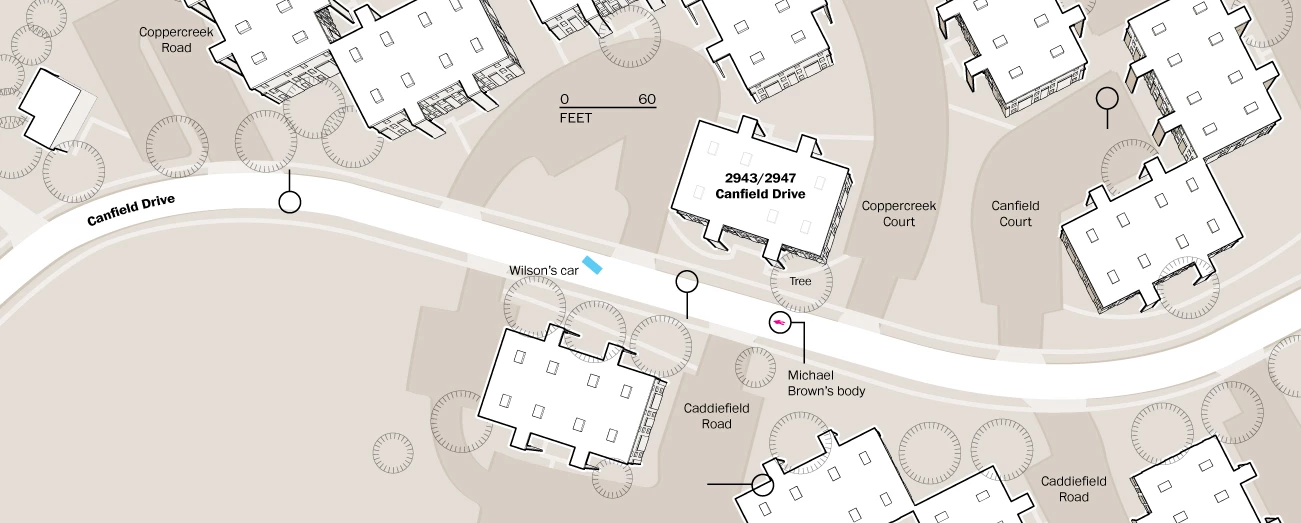
First witness, the chief investigating officer. Establish a scale map of the area and the locations of Darren Wilson’s vehicle, Darren Wilson’s claimed position and the final location of Michael Brown.
A map something like:
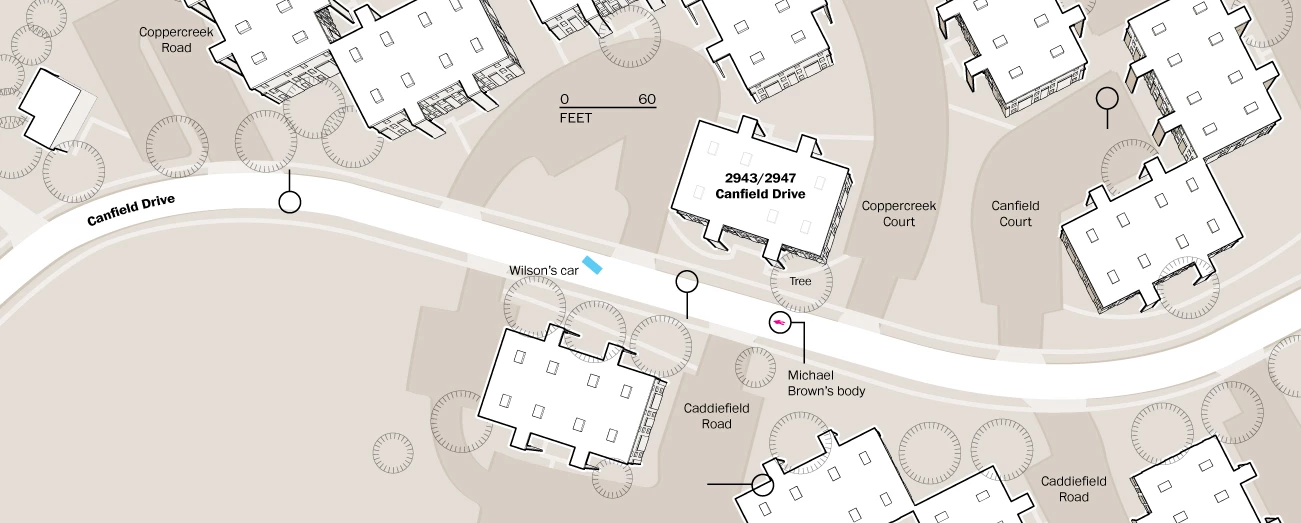
(See this map in full at: http://www.washingtonpost.com/wp-srv/special/national/ferguson-witness-map/, it was authored by Richard Johnson.)
Elicit the following facts from the chief investigating officer:
- Michael Brown was in fact unarmed.
- Officer Darren Wilson said that he shot Michael Brown. (hearsay is admissible in grand jury proceedings)
- Officer Darren Wilson was also armed with police issued Mace at the time of the shooting.
- Officer Darren Wilson had pursued Michael Brown for over 100 feet from any initial contact.
- Michael Brown’s body had no traces of Mace on it.
- Officer Darren Wilson’s issued Mace was unused.
- Michael Brown was shot eight (8) times, three of them in the head.
- The medical examiner concluded that Michael Brown died as a result of gun shot wounds on 9 August 2014.
Unnecessary but to give the grand jury the human side of the story, call the witness from the second floor of the apartment building who testified to the grand jury:
Volume 8 – September 30, 2014 – Page 114
…
23 A Okay. Then my brother noticed, he said
24 wait a minute, looks like they’re struggling. We
25 are looking at the car, we can see them tussling,
Volume 8 – September 30, 2014 – Page 115
1 all right. His head was above the truck for a
2 moment and then it went below it.
3 Q Okay.
4 A All right. And it was still tussling.
5 His friend had backed up a step back on the
6 sidewalk, then we heard a shot. His friend ran this
7 direction, Michael ran to this driveway right here,
8 beside this building.
9 Q Just so we can be clear, this street is
10 Copper Creek Court?
11 A Right.
12 Q So you are saying, you had the pointer,
13 the little laser ——
14 A Right, right here.
15 Q —— at the corner of Canfield Drive and
16 Copper Creek Court?
17 A Right, he had ran towards this way. As
18 he’s running ——
19 Q He’s running east down Canfield?
20 A As he’s running this way, the officer got
21 out of his truck, came around from the back, got to
22 this side where he was now on the driver’s side
23 because he had a clear line of Michael over here.
24 Then he assumed his position with the
25 pistol. As he turned around, as he came around, he
Volume 8 – September 30, 2014 – Page 116
1 was coming up with the gun. He held the gun up like
2 this. (indicating) When he got to here, Michael was
3 standing right on the grass and he was like looking
4 down at his body.
5 Q Okay. Let me stop you here. At this
6 point have you seen anything in Michael’s hands?
7 A No.
8 Q When he was stopped, when they were
9 talking down the street, did you see anything in his
10 hands?
11 A No.
12 Q How about the other boy, anything in his
13 hands?
14 A No.
15 Q They weren’t carrying anything that you
16 saw?
17 A No.
18 Q And then you said, you know how important
19 some of this gesturing has been, right?
20 A Uh—huh, right.
21 Q So they are here to actually witness what
22 you are going to do. And so you say when Michael
23 Brown gets to, is he in the grass actually?
24 A He’s is standing at the very edge. Okay.
25 The driveways are blacktop, he is stopped right at
Volume 8 – September 30, 2014 – Page 117
1 the blacktop right, at the very edge.
2 Q Okay.
3 A His back was turned to the officer.
4 Q Okay.
5 A And he had his hands like this, like he’s
6 looking down at his body to see.
7 Q Okay. Can I ask you to stand up that will
8 really help them to see what you’re doing and he’s
9 stopped now?
10 A He’s stopped with his back towards the
11 officer and he stopped and he was doing this. As he
12 was trying to see where he was shot.
13 Q Okay.
14 A All right.
15 Q Uh—huh.
16 A As he was turning, at that time the
17 officer had already been around to the back of his
18 truck and got into his spot. By the time he got
19 there, while Michael was there, he was slowly
20 turning around and the officer said stop. When
21 Michael turned around, he just put his hands up like
22 this. They were shoulder high, they weren’t above
23 his head, but he did have them up. He had them out
24 like this, all right, palms facing him like this.
25 The officer said stop again. Michael
Volume 8 – September 30, 2014 – Page 118
1 then took a step, a few steps it took for him to get
2 from that blacktop to the street. When he stepped
3 out on the street, the officer said stop one more
4 time and then he fired. He fired three to four
5 shots. When he hit him, he went back. Can I stand?
6 Q Sure.
7 A When he hit him he, did like this, and he
8 went like, like his balance —— he started staggering
9 and he looked up at the officer like why.
10 Q Now, just to be clear, you can’t hear him
11 say anything?
12 A I can’t hear him say that, but he’s
13 looking at him and he is doing, you know. So then
14 as he’s stopped, he’s trying to steady, he starts
15 staggering, my brother says, he’s not going to stand
16 up, he’s getting ready to fall, he’s getting ready
17 to fall.
18 He looks like he was trying to stay
19 on his feet, and he started staggering toward the
20 police officer and he still had his hands up.
21 At some point between the officer’s
22 truck, which by that time this is about 30, 35 feet,
23 when he reached out into the street, he started
24 walking toward the officer, the officer took three
25 steps back and he yelled out stop to Michael again
Volume 8 – September 30, 2014 – Page 119
1 three times.
2 Michael’s steadily walking toward
3 him. More or less to me and to my brothers, he was
4 staggering.
5 Q Okay. To your brothers, did you have more
6 than one brother?
7 A Well, I mean my brother. I didn’t mean to
8 say brothers, my brother. He was staggering, you
9 know. And as he was staggering forward, his head,
10 his body kind of went down at an angle. He was like
11 this, more or less fighting to stay up. You could
12 see his legs wobbling.
13 Q Were his hands the way you had them?
14 A His hands were coming down like this, all
15 right. And he had his head up and he’s facing the
16 officer like this and he is steadily moving, and the
17 officer was moving back, stop. He yelled stop the
18 third time, he let off four more shops, but as he
19 was firing, Michael was falling. After he stopped
20 firing, Michael, he went down face first, smack.
What do you think? Probable cause for:
- Darren Wilson (a person)
- intentionally shot – 8 times (knowingly causes)
- to kill Michael Brown (another person) or
- to inflict serious injury on Michael Brown (another person)
- and Michael Brown dies (death)
Unless you think a police officer yelling “stop” is a license to kill, there is more than enough evidence for probable cause to indict for second degree murder. Total grand jury time, perhaps a day or a day and a half.
Should the grand jury ask about self-defense, lawful arrest, etc. the proper response is that all of those are great questions but under Missouri law, the responsibility to answer those questions resides with the trier of fact, whether it is a judge or jury. In a trial, both sides are represented with a judge to insure that all sides have an opportunity to present their side. In a grand jury proceeding, only the State is represented so it would be unfair for the State to attempt to represent both sides.
Don’t be fooled into “accepting” the grand jury’s decision. Another grand jury can and should be chosen to properly consider the Michael Brown shooting. Even more importantly, all those connected to the first grand jury should be investigated to determine who decided to throw the first grand jury. I can’t believe that an assistant prosecutor made that decision all on their own.