The trials and tribulations of hiring hackers, much less hiring them by governments, are but a quick search away. A few of the articles I have encountered: Hiring hackers: The good, the bad and the ugly, Top 10 Pros and Cons of Hiring Hackers to Enhance Security, and, Hiring a hacker: Why and how you should do it.
These posts and others suffer from a lack of imagination in harnessing hackers for bettering government security.
Governments want fewer cybersecurity risks. Hackers want less risk from their hacking activities. Here’s one way to lessen the risks on both sides:
- Government creates a PGP key for encryption of method and proof of hack on a government information system.
- The encrypted package is signed by the hacker in question for proof of ownership of that hack.
- Uploading of the encrypted package to a public website, along with which a hacker can claim their handle, automatically grants the hacker immunity for the hack and use of its results. Additionally, the hack cannot be used in any other prosecution for any purpose.
- The government can solicit solutions for submitted hacks from the submitting hacker(s) or from hackers more generally.
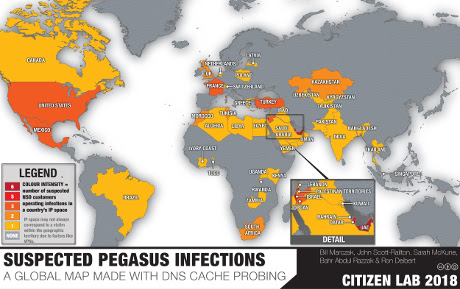
Governments, any government, are already hemorrhaging data. Anyone who says differently is selling a mythical security solution. Be forewarned.
The proposed hack/immunity system gives governments notice of hacks and their specifics, in exchange for immunity in the unlikely event that anyone will be prosecuted for a hack.
Moreover, the privacy of hackers is preserved since they must produce the key to verify the signing of the encrypted package, which they would only do in case of a prosecution based on or using that hack.
The cybersecurity community as a whole gains greater reliability of breach information compared to:
…This year’s report is based on a global survey conducted by 451 Research during October and November of 2017.
In contrast to last year’s report, we surveyed 1,200+ senior security executives from across the globe (up from 1,100), including respondents from key regional markets in the U.S., U.K., Germany, Japan, Sweden, the Netherlands, Korea and India. We also surveyed key segments within those countries including federal government, retail, finance and healthcare. While all 1,200 respondents have at least some degree of influence in data security decision-making, more than one-third (34%) have ‘major’ influences on these decisions and nearly half (46%) have sole decision-making authority.
… 2018 THALES DATA THREAT REPORT
Misgivings over the trustworthiness of hackers is highly selective. Thales relies on people with an interest in their fails looking similar to everyone else’s. Rather odd “research” technique.
PS: Should anyone (US prosecutors, FBI, etc.) protest the automatic granting of immunity, ask them for their prosecution statistics versus the number of known breaches in their districts.
You can waste money on by chance prosecutions and cybersecurity myths or, you can correct your systems against the best hackers in the world. Your call.