Pentagon’s Multibillion-Dollar DEOS Contract is Guaranteed for Microsoft
High-five traffic saturated networks between groups of North Korean, Chinese and Russian hackers when they read:
In the coming weeks, the Pentagon—through its partner, the General Services Administration—will bid out a cloud-based contract for enterprisewide email, calendar and other collaboration tools potentially worth as much as $8 billion over the next decade.
…
Yet former defense officials, contracting analysts and industry experts tell Nextgov the Defense Enterprise Office Solutions contract is one that tech giant Microsoft—with its Office 365 Suite—simply cannot lose.
Yes, the Pentagon, through a variety of bidders, all of who offer Microsoft based solutions, is adopting a hostile adoption strategy, described as:
According to Defense Department spokeswoman Elissa Smith, the intent is for DEOS to replace all the disparate, duplicative collaboration tools Defense Department agencies use around the world. Components, including the Army, Navy and Air Force, “will be required” to use the same cloud-based business tools.
“It is expected that DEOS will be designated as an enterprise solution for DOD-wide adoption and organizations,” Smith told Nextgov. “Components that have already implemented different solutions with similar functionality will be required to migrate to DEOS.”
You may remember how successful the FBI Virtual Case File project was, $170 million in the toilet, where local FBI offices were to be “forced” to migrate to a new system. Complete and utter failure.
Undeterred by previous government IT failures, the Pentagon is upping the stakes 47 X the losses in the FBI Virtual Case File project and, even more importantly, risking national security on hostile adoption of an unwanted product.
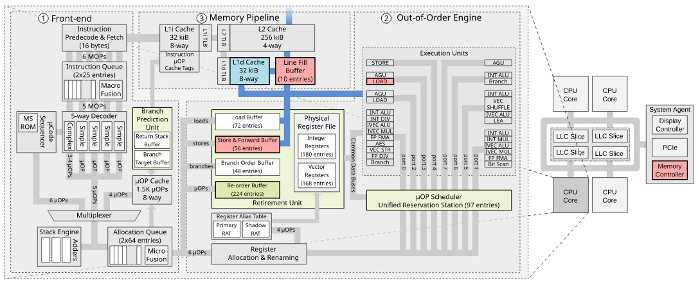
If that weren’t bad enough, the Office 365 Suite offers a security single point of failure (SPOF). Once the system is breached for one instance, it has been breached for all. Hackers can now abandon their work on other systems and concentrate on Microsoft alone. (A thanks on their behalf to the Pentagon.)
Hackers are unlikely to take up my suggestion because an eight year slog to complete failure leaves non-Microsoft systems in operation during and past the project’s failure date. Not to mention that a hostile transition to an unwanted system is likely to leave openings for exploitation. Happy hunting!
 Links to several paid proxy services are listed as well.
Links to several paid proxy services are listed as well.