Fake News, Facts, and Alternative Facts by Will Potter, Josh Pasek, and Brian Weeks.
From “About this course:”
How can you distinguish credible information from “fake news”? Reliable information is at the heart of what makes an effective democracy, yet many people find it harder to differentiate good journalism from propaganda. Increasingly, inaccurate information is shared on Facebook and echoed by a growing number of explicitly partisan news outlets. This becomes more problematic because people have a tendency to accept agreeable messages over challenging claims, even if the former are less objectively credible. In this teach-out, we examine the processes that generate both accurate and inaccurate news stories, and that lead people to believe those stories. We then provide a series of tools that ordinary citizens can use to tell fact from fiction.
To honor the exhortations “use critical thinking,” here are some critical thoughts on course description for “Fake News, Facts, and Alternative Facts.”
How can you distinguish credible information from “fake news”?
The description starts with black and white, normative classifications, one good, “credible information,” and one bad,“fake news.” Information other than being alive or dead is rarely that clear cut. As Tom Petty recently proved, even being dead can be questionable.
You are being emotionally primed to choose “credible information,” as opposed to evaluating information to determine the degree, if any, it should be trusted or used.
Reliable information is at the heart of what makes an effective democracy,
A remarkable claim, often repeated but I have never seen any empirical evidence for that proposition. In critical thinking terms, you would first have to define “reliable information” and “effective democracy.” Then using those definitions, provide empirical evidence to prove that in the absence of “reliable information” democracy is ineffective and with “reliable information” democracy is effective.
It’s an easy claim to make, but in the context of a critical thinking course, isn’t more required than repeating popular cant?
I’ll grant many theories of democracy are predicated upon “reliable information but then those theories also posit equal treatment of all citizens, another popular fiction.
yet many people find it harder to differentiate good journalism from propaganda.
As opposed to when? What is the baseline for when people could more easily “…differentiate good journalism from propaganda…?” Whenever you hear this claim made, press for the study with evidence to prove this point.
You do realize any claiming such a position considers themselves capable of making those distinctions and you are very likely in the class of people who cannot. In traditional terminology, that’s called having a bias. In favor of their judgment as opposed to yours.
Increasingly, inaccurate information is shared on Facebook and echoed by a growing number of explicitly partisan news outlets.
You know the factual objections by this point, what documentation is there for an increase in “inaccurate information” (is that the same as false information?) over when? When was there less inaccurate information. Moreover, when were there fewer “explicitly partisan news outlets?”
By way of example, consider these statements about Jefferson during the presidential election in 1800:
…
In the election of 1800, ministers spread rumors that Jefferson held worship services at Monticello where he prayed to the “Goddess of Reason” and sacrificed dogs on an altar. Yale University president Timothy Dwight warned that if he became president, “we may see the Bible cast into a bonfire.” Alexander Hamilton asked the governor of New York to take a “legal and constitutional step” to stop the supposed atheist vice president from becoming head of state. Federalists who opposed him called him a “howling atheist,” a “manifest enemy to the religion of Christ,” a “hardened infidel,” and, for good measure, a “French infidel.” As Smith describes it, insults like these were issued forth from hundreds of pulpits in New England and the mid-Atlantic. When Jefferson won the election, many New England Federalists buried their Bibles in their gardens so the new administration would not confiscate and burn them.
…
It may just be me but it sounds like there was “inaccurate information” and “explicitly partisan news outlets” available during the presidential election of 1800.
When anyone claims there is more “inaccurate information” or “explicitly partisan news outlets,” ask for percentage evidence against some base period.
Surely if they are devoted to “credible/reliable information,” they would not make such statements in the absence of facts to back them up. Yes?
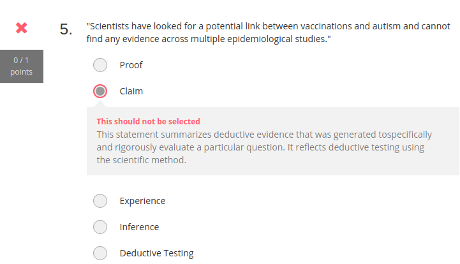
This becomes more problematic because people have a tendency to accept agreeable messages over challenging claims, even if the former are less objectively credible.
People accepting messages they find agreeable is a statement of how people process information. Thinking Fast, Thinking Slow, Kahneman.
The claim goes off the rails with “…even if the former are less objectively credible.”
Where does “…less objectively credible.” come from? It’s a nice sleight of hand but never fall for anyone claiming an “objective” context. It doesn’t, hasn’t and won’t ever exist.
You can make claims from the context of a community of people, scholars, experts, etc., that is every claim originates in shared values and worldview. (See Stanley Fish if you are interested in the objectivity issue.
As with all such claims, the authors have a criteria for “objectively credible” they want you to use in preference to other criteria, suggested by others.
There’s nothing wrong with advocating a particular criteria for judging information, we can all do no more or less. What I object to is cloaking it in the fiction of being beyond a context, to be “objective.” Let us all put forth our criteria and contend for which one should be preferred on an equal footing.
In this teach-out, we examine the processes that generate both accurate and inaccurate news stories, and that lead people to believe those stories. We then provide a series of tools that ordinary citizens can use to tell fact from fiction.
I can almost buy into “accurate” versus “inaccurate” news stories but then I’m promised “tools” to enable me to “…tell fact from fiction.”
Hmmm, but “Who is this class for:” promises:
This course is aimed at anyone who wants to distinguish credible news from “Fake News” by learning to identify biases and become a critical information consumer.
I don’t read “…learning to identify biases…” as being the same thing as “…tools…to tell fact for fiction.”
The latter sounds more like someone is telling me which is fact and fiction? Not the same as being on my own.
I’m enrolling in the course now and will have more comments along the way.
The crucial point here is that “critical thinking” should be universally applied, especially so to discussions of critical thinking.