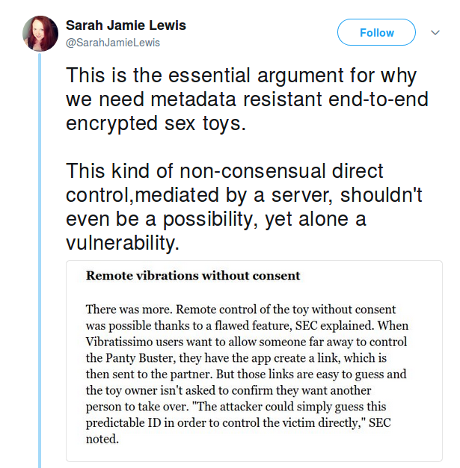
Thursday began innocently enough and then I encountered:
The tumult of articles started (I think) with: Internet of Dildos: A Long Way to a Vibrant Future – From IoT to IoD, covering security flaws in Vibratissimo PantyBuster, MagicMotion Flamingo, and Realov Lydia, reads in part:
…
The results are the foundations for a Master thesis written by Werner Schober in cooperation with SEC Consult and the University of Applied Sciences St. Pölten. The first available results can be found in the following chapters of this blog post.The sex toys of the “Vibratissimo” product line and their cloud platform, both manufactured and operated by the German company Amor Gummiwaren GmbH, were affected by severe security vulnerabilities. The information we present is not only relevant from a technological perspective, but also from a data protection and privacy perspective. The database containing all the customer data (explicit images, chat logs, sexual orientation, email addresses, passwords in clear text, etc.) was basically readable for everyone on the internet. Moreover, an attacker was able to remotely pleasure individuals without their consent. This could be possible if an attacker is nearby a victim (within Bluetooth range), or even over the internet. Furthermore, the enumeration of explicit images of all users is possible because of predictable numbers and missing authorization checks.
…
Other coverage of the vulnerability includes:
- ‘Panty Buster’ Toy Left Private Sex Lives Of 50,000 Exposed (Forbes)
- A Remote-Controlled Sex Toy Exposed 50,000 People’s Sex Lives, Says Security Company (The Daily Caller)
- Bluetooth ‘Panty Buster’ smart mock-cock fails penetration test (The Register)
- This smart vibrator can be ‘easily’ hacked and remotely controlled by anyone (ZDNet)
- The internet of dildos is here, and it’s vulnerable as hell (Yahoo! Finance)
- The ‘internet of dildos’ is not very secure (LMTonline)
Vibratissimo product line (includes the PantyBuster).
The cited coverage doesn’t answer how to incentivize end-to-end encrypted sex toys?
Here’s one suggestion: Buy the PantyBuster or other “smart” sex toys in bulk. Re-ship these sex toys, after duly noting their serial numbers and other access information, to your government representatives, sports or TV figures, judges, military officers, etc. People whose privacy matters to the government.
If someone were to post a list of such devices, well, you can imagine the speed with sex toys will be required to be encrypted in your market.
Some people see vulnerabilities and see problems.
I see the same vulnerabilities and see endless possibilities.