Open Source Data Jeopardizing Cleared Personnel: Intelligence Operations Outsmarted by Technology by Alexander H. Georgiades.
Abstract:
The availability and accessibility of Open Source Intelligence (OSINT) combined with the information from data breaches has affected cleared personnel in the United States Intelligence Community (IC) and Department of Defense (DoD) who conduct and support intelligence operations. This information when used in conjunction with biometric detection technology at border crossings has greatly improved the likelihood of cleared personnel from the United States Government (USG) of being identified and targeted by adversaries. The shift from traditional Tactics, Techniques, and Procedures (TTPs) used by cleared personnel (either operating in an overt or covert status) during the Cold War when biometric technology was not an obstacle, has caught the United States government intelligence services off-guard when conducting sensitive missions Outside of the Continental United States (OCONUS).
The consequences of not maintaining updated software and hardware standards have already affected U.S. intelligence operations and exposed cleared personnel. The computer breach at the Office of Personnel and Management (OPM), where millions of sensitive records from cleared personnel in the private and public sectors is the most recent example. This unprecedented loss of Personally Identifiable Information (PII) has been the unfortunate wakeup call needed for decision makers in the United States government to reevaluate how they handle, collect, store, and protect the information of cleared personnel in this digital age.
The analysis of competing hypothesis and other predictive analytical methods will be used to evaluate the data available to adversaries who target cleared personnel and the intelligence operations they support. Case studies, news articles, books, government, and industry reports will be used as supporting evidence to illustrate how the growth in biometric detection technology use in conjunction with the availability of OSINT and material from data breaches adversely affect intelligence operations.
The amount of information available to adversaries is at an unprecedented level. Open source forums provide detailed information about cleared personnel and government TTPs that can be used by adversaries to unravel intelligence operations, target cleared personnel, and jeopardize USG equities (such as sources and methods) in the field. The cleared workforce must learn from mistakes of complacency and poor tradecraft in the past to develop new methodologies to neutralize the effectiveness of adversaries who use OSINT and biometric technology to their advantage.
Social media use by cleared employees who reveal too much operational information about themselves or the projects they work on is one of the gateways that can be easily closed to adversaries. Cleared personnel must be mandated to limit the amount of information they publish online. By closing the door to social media and preventing the personal and professional lives of the cleared workforce from being used to target them, adversaries would not be as effective in jeopardizing or exposing intelligence operations overseas. Increased Operational Security (OPSEC) procedures must also be mandated to protect the programs and operations these cleared personnel work on, with an emphasis on covert officers who use false personas when operating overseas.
The information bridges that were created after September 11, 2001 to increase collaboration must be reevaluated to determine if the relaxation of classified information safeguards and storage of sensitive information is now becoming detrimental to USG intelligence operations and cleared personnel.
As you know, I have little sympathy for the Intelligence Community (IC), creators of the fishbowl in which we commonly reside. Members of the IC sharing that fate, has a ring of justice to it.
This thesis offers a general overview of the problem and should be good to spark ideas of open source intelligence that can be used to corroborate or contradict other sources of intelligence.
By way of example, educational records are easy enough to edit and convincing to anyone not aware they have been edited.
On the other hand, original and digitized year books or similar contemporary resources, are not so easily manipulated.
As I say that, tracking every child from first grade through the end of their academic career, is eminently doable, with the main obstacle being acquisition of the original yearbooks.
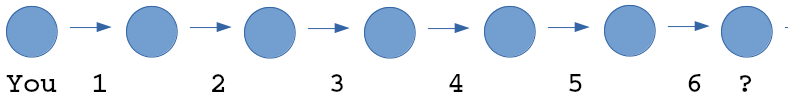
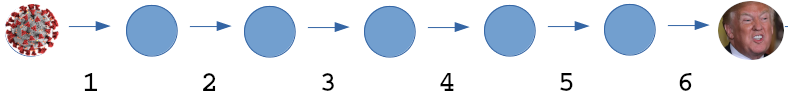
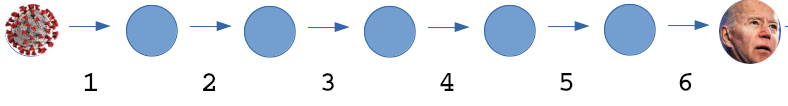
Cross-referencing other large collections of photos and the project starts to sound useful to any number of governments, especially those worried about operatives from Western countries.
Are you worried about Western operatives?